SSL/TLS auditor to enforce high-grade transport encryption
Automated monitoring for your mail server's SSL/TLS certificates and cipher suites. Audit for Perfect Forward Secrecy, track certificate transparency, and mitigate transport-layer vulnerabilities.
Certificate lifecycle
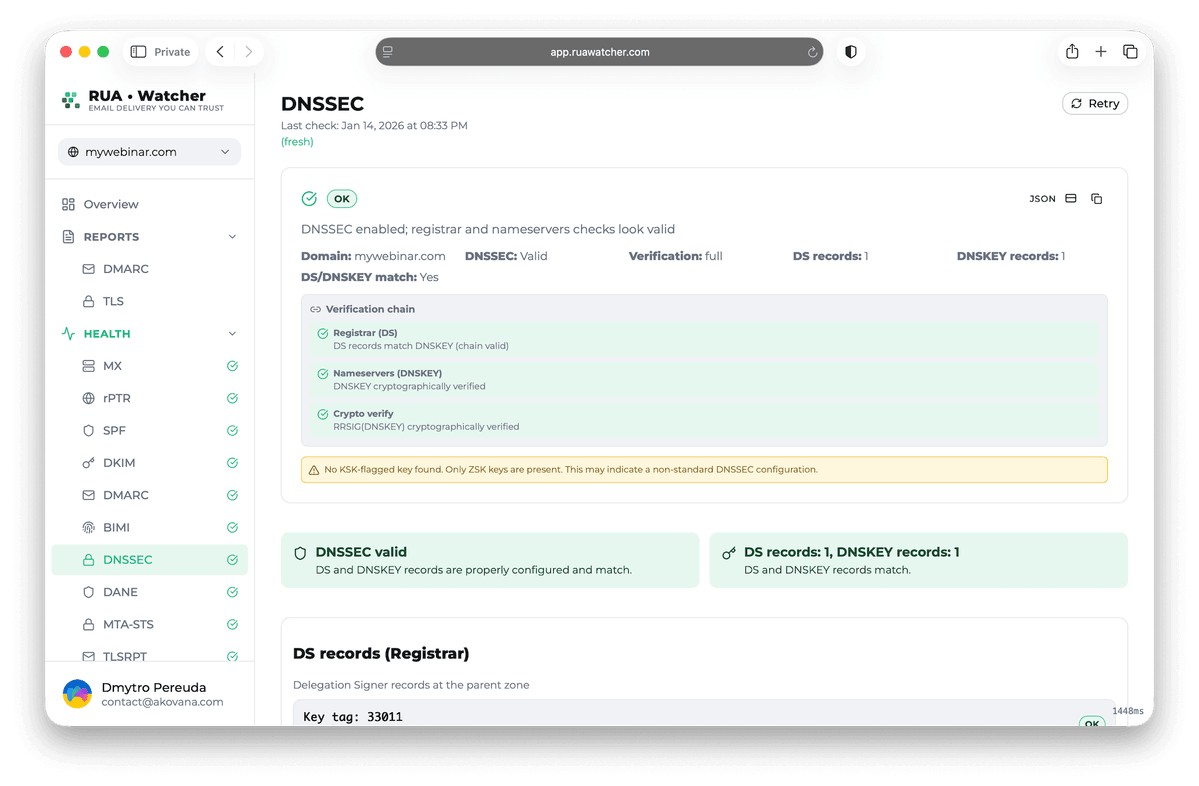
Monitors SSL/TLS certificate validity, expiration, and chain of trust. Sends proactive alerts on revocation signals and Certificate Transparency logs
- Chain of trust validation
- Revocation signal tracking
- CT log monitoring
Comprehensive mail server security auditor
Our auditor tools help you enforce robust security standards and maintain a secure email infrastructure that meets modern requirements.
Automatic scanning
Continuous status checks
PFS verification
Perfect Forward Secrecy
Hostname validation
Correct certificate matching
OCSP stapling
Real-time revocation check
Expiration alerts
Multi-channel notifications
Historical reports
Track security upgrades
Securing your mail servers in 3 steps
RUA•Watcher makes it easy to maintain high-grade encryption across your entire infrastructure.
Handshake audit
Our system performs a recursive SSL/TLS handshake to identify supported ciphers and protocol versions
Identify vulnerabilities
Review the security report for weak keys, missing PFS, or lack of Certificate Transparency (CT) compliance
Monitor & alert
Enable alerts to receive immediate notifications about certificate issues or security regressions
SSL/TLS monitoring FAQ
Common questions about email encryption and server security.
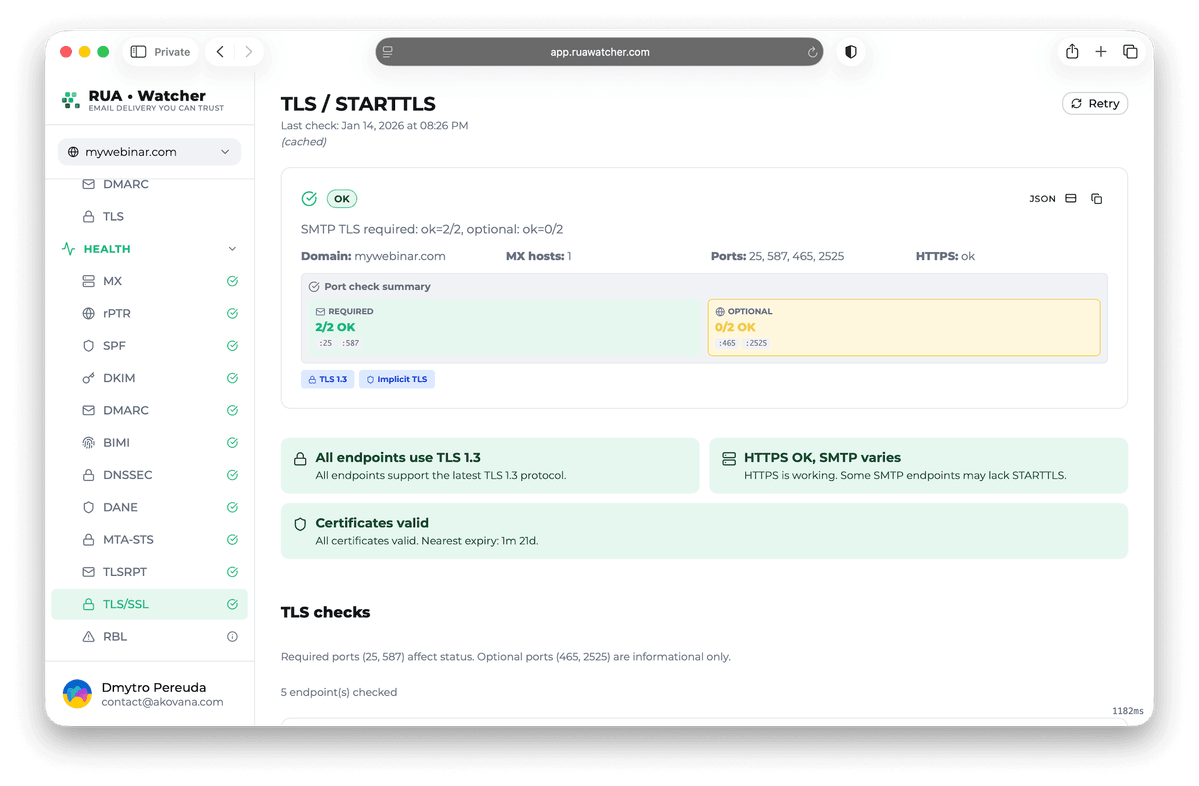
STARTTLS on ports 25 and 587 upgrades an unencrypted connection to a secure one, while Implicit TLS on port 465 is encrypted from the start. We monitor both to ensure your servers follow modern encryption standards.
Yes. For MTA-STS policy hosting, we audit HSTS (HTTP Strict Transport Security) headers to ensure your policy cannot be downgraded during delivery.
SSL/TLS encrypts the connection between mail servers, ensuring that your emails cannot be intercepted or read by unauthorized parties during transit.
If a certificate expires, other mail servers may refuse to send you email or mark it as insecure. This can lead to delivery failures and broken MTA-STS policies.
By default, we scan your mail server ports (25, 465, 587) every hour. Enterprise accounts can increase the frequency for critical infrastructure.
Ready to harden your mail transport security?
Validate TLS on every hop, confirm modern ciphers and certificates, and get alerts when encryption settings drift or expire