MTA-STS auditor to mitigate MITM attacks and enforce encrypted delivery
Transition safely from opportunistic TLS to enforced encryption per RFC 8461. Our auditor validates policy synchronization, monitors TLS-RPT signals, and helps prevent transport-layer interception.
Policy governance
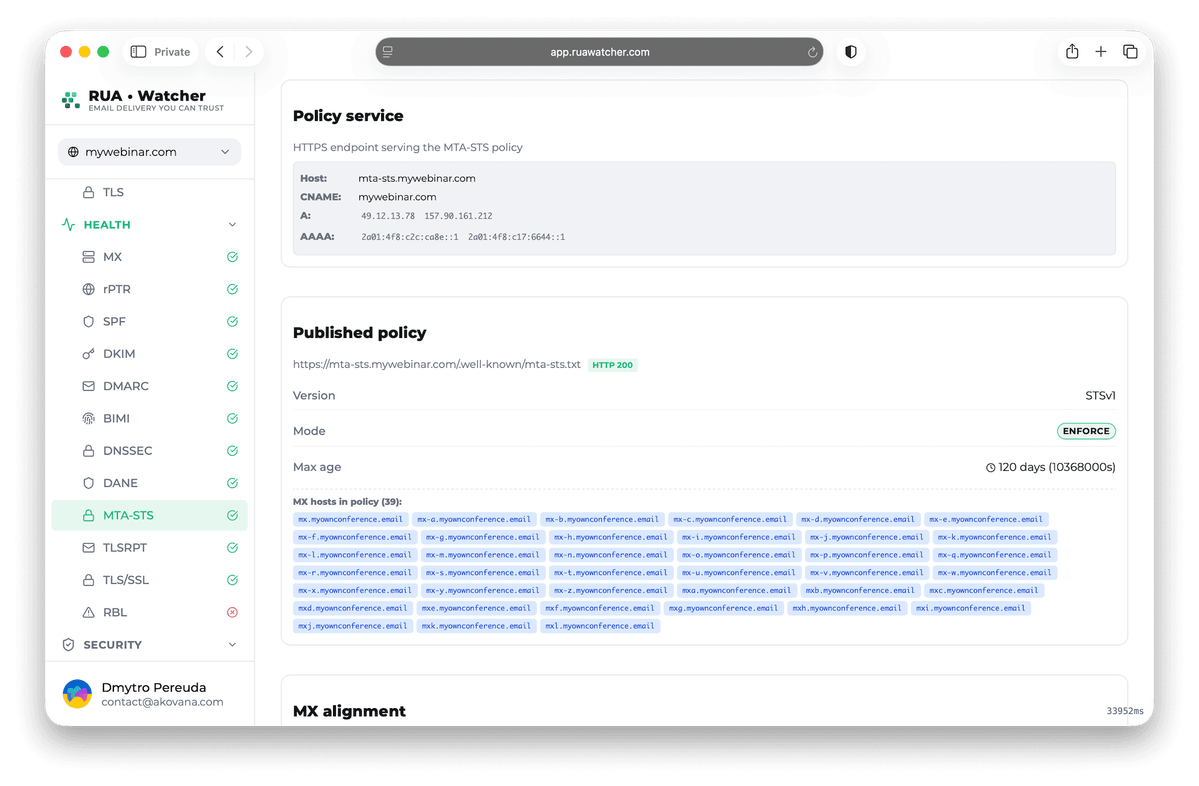
Audits your MTA-STS policy file for RFC 8461 compliance by verifying HTTPS endpoint security, certificate chain validity, and policy syntax
- HTTPS policy hosting audit
- RFC-compliant syntax check
- Endpoint certificate monitoring
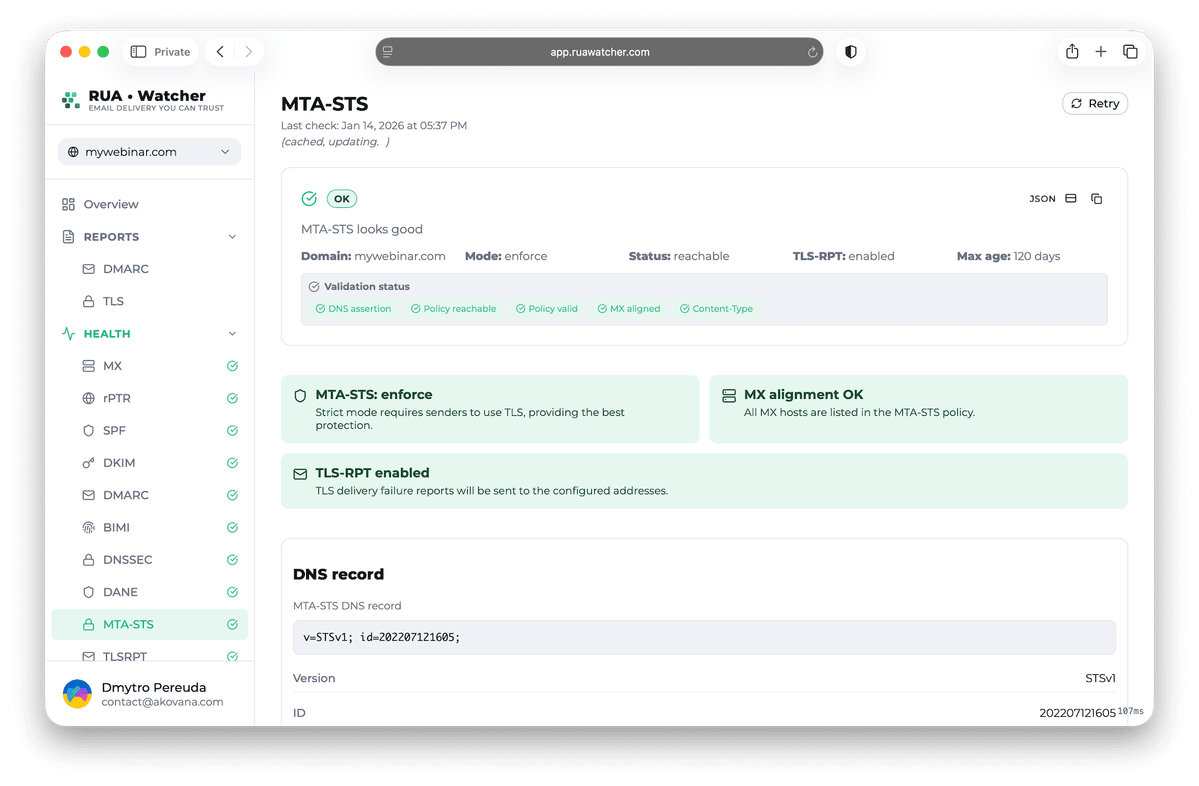
MTA-STS validator for strict transport security
Our validator tools help you move from standard opportunistic TLS to strict, enforced encryption and mitigate MITM attacks.
Real-time validator
Instant configuration audit
Policy synchronizer
Manage record IDs
Certificate audit
Verify HTTPS endpoint
Enforcement tracker
From testing to enforce
Error diagnostics
Pinpoint delivery failures
Team alerts
Policy health alerts
Enforce MTA-STS in 3 steps
Transition safely from unencrypted to enforced transport security.
Policy ingestion
Our system recursively scans your domain to discover existing MTA-STS policies and DNS records
Synchronize IDs
Verify that your DNS STS-id matches your policy content to ensure sending servers pick up the latest rules
Signal-driven enforcement
Use TLS-RPT signals to safely move from testing to enforce mode without risking legitimate mail delivery
MTA-STS FAQ
Common questions about Mail Transfer Agent Strict Transport Security.
MTA-STS is a security standard that allows domain owners to declare their support for TLS encryption and specify whether sending servers should refuse delivery if TLS is not available. Using a dedicated checker helps ensure your policy and DNS records are correctly synchronized.
The id field in the _mta-sts TXT record tells sending servers when your policy has changed. If you update your policy file but do not change the id in DNS, servers will continue using the cached version.
DMARC protects the *content* and *sender identity* of the email. MTA-STS protects the *transport* (the pipe) the email travels through, specifically preventing interception.
TLS-RPT provides the feedback loop needed to know if your MTA-STS policy is causing delivery failures, allowing you to fix issues before they impact your business.
In testing mode, sending servers report TLS failures but still deliver mail even without encryption. In enforce mode, servers must refuse delivery if a secure TLS connection cannot be established. Start with testing to identify issues, then switch to enforce once TLS-RPT signals confirm stable encrypted delivery.
Ready to enforce encrypted mail delivery?
Validate your MTA-STS policy, confirm TLS requirements, and get alerts when DNS or HTTPS changes can weaken transport security