DMARC analyzer and monitoring platform that brings clarity to email authentication
Our analyzer brings clarity to aggregate and forensic reports, checks SPF/DKIM alignment, stops spoofing, and helps you reach compliance with live monitoring
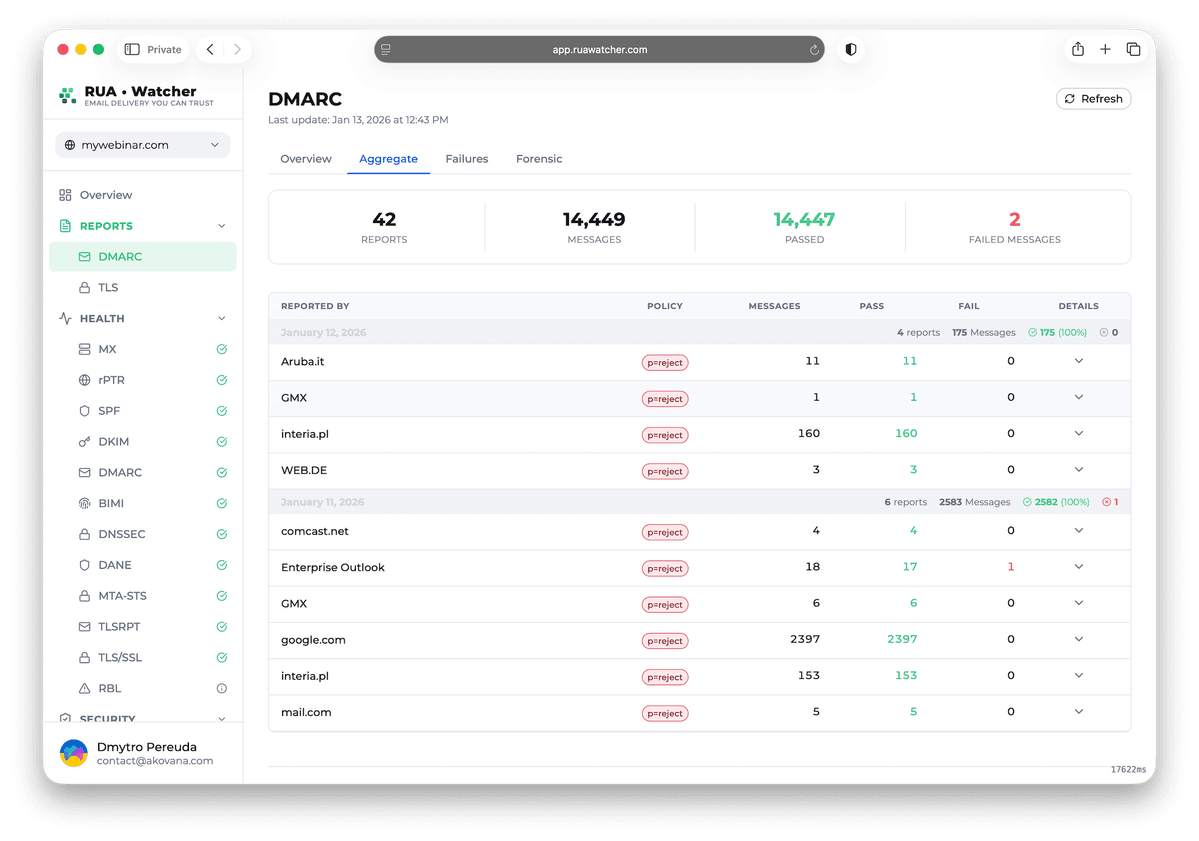
Aggregate reports
Aggregate reports reveal authentication patterns at scale. Review DMARC XML from major ISPs to understand traffic volume, authentication status, and alignment health
- DMARC XML parsing
- Daily aggregation
- Traffic by ISP
- SPF and DKIM alignment
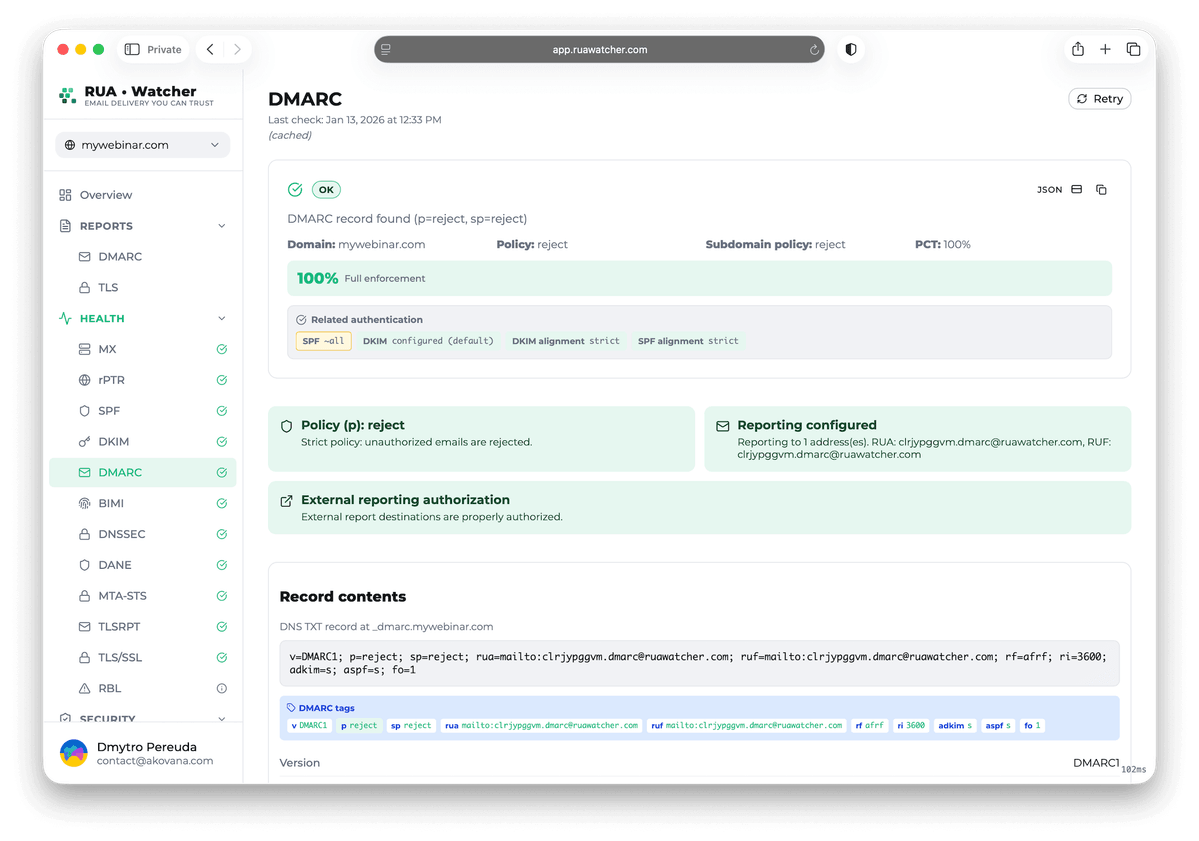
DMARC monitoring and email security validation
Technical tooling for DMARC enforcement, authentication visibility, and sender reputation control. Built for teams running high-volume email infrastructure who require reliable domain-level signals
DMARC XML pipeline
High volume report ingestion
Sender reputation watch
Domain and IP risk signals
Alignment validation
SPF and DKIM alignment status
Compliance reporting
Scheduled evidence and summaries
Team access control
Roles and domain scoping
Alerting and automation
Slack email and webhooks
DMARC compliance in three steps that guide you from monitoring to p=reject
RUA•Watcher helps you turn raw DMARC reports into enforceable policy so you can block spoofing and protect deliverability
Start monitoring
Publish a DMARC record with p=none so reports start flowing. We ingest and normalize XML from mailbox providers and map sources to your domain
Validate alignment
Review legitimate senders and fix SPF and DKIM alignment issues. Track failures by source and confirm what passes before you tighten policy
Enforce p=reject
Move from p=quarantine to p=reject once alignment is stable. Stop spoofed mail while keeping approved traffic authenticated and deliverable
DMARC monitoring & reporting FAQ
Technical details that explain DMARC deployment, report processing, and the workflows that help you enforce policy compliance
Mailbox providers usually send aggregate reports once every 24 hours. Your dashboard will show the first normalized data within 24 to 48 hours after the record goes live.
Yes. Aggregate reports show overall authentication patterns, while forensic reports provide samples of messages that failed authentication. Our system automatically redacts personally identifiable information from these reports to ensure GDPR compliance while preserving technical headers for analysis.
Starting with p=none lets you collect data without impacting mail delivery. This approach helps you identify legitimate senders like SaaS platforms that are not yet fully aligned, giving you time to fix configuration issues before tightening enforcement.
Our processing pipeline detects traffic that was forwarded through mailing lists or aliases and separates legitimate delivery paths from actual domain impersonation attempts. This helps you avoid false positives and ensures that you only see data from your domain.
Yes. You can access original XML files or export CSV reports. We also support automated CSV delivery via email or API for integration with your internal SIEM or security dashboards.
Ready to reach DMARC compliance?
Stop guessing and start enforcing. Join engineers who use RUA•Watcher to move safely to p=reject and secure their domain reputation