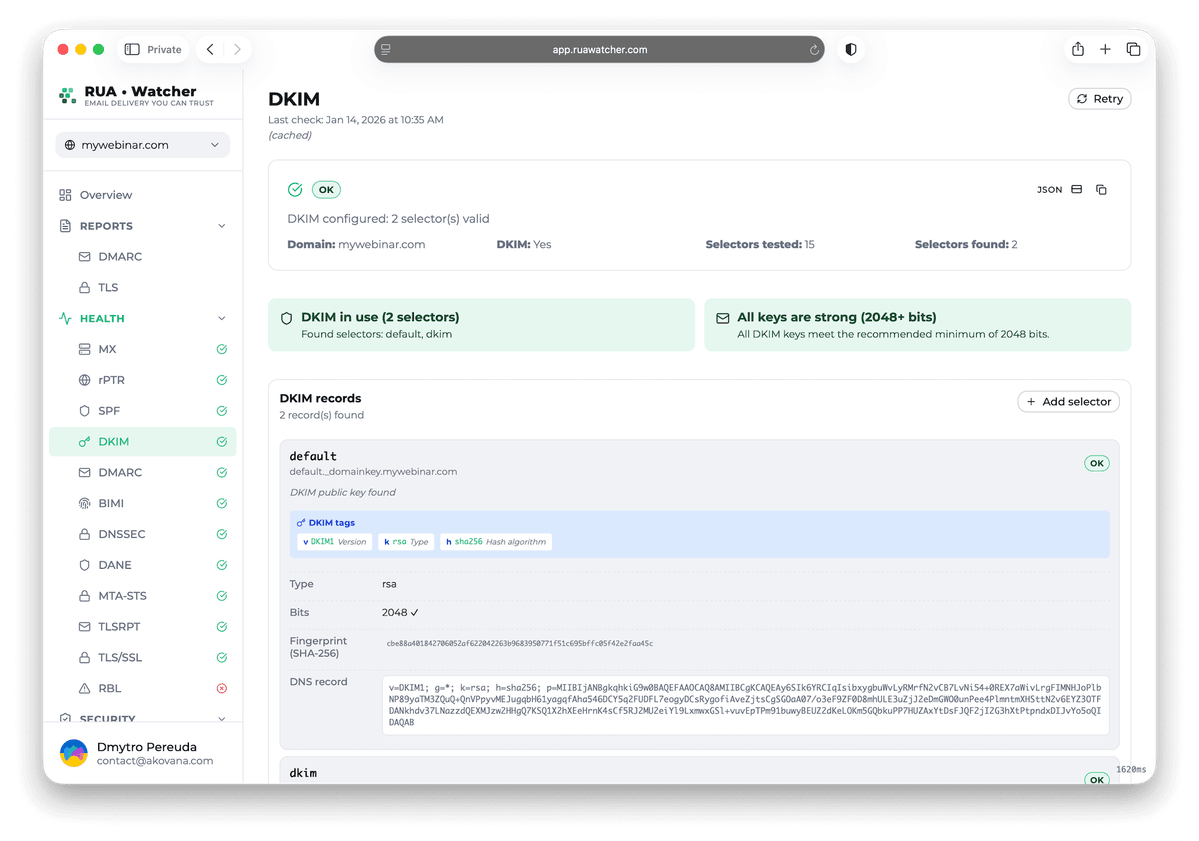
DKIM Key Manager for Selector Monitoring & Validation
Take full control of your DKIM infrastructure with our key manager. Monitor selectors, validate key strength for both RSA and Ed25519, and detect misconfigurations before they impact deliverability. Ensure cryptographic alignment through automated posture auditing
Security auditing
Audit your DKIM security posture against modern standards. Detect weak keys, verify cryptographic algorithms, and surface risky tag combinations before they impact email authentication and inbox placement
- RSA 2048+ validation
- Ed25519 algorithm checks
- Policy drift detection
Enterprise-Grade DKIM Lifecycle Validation
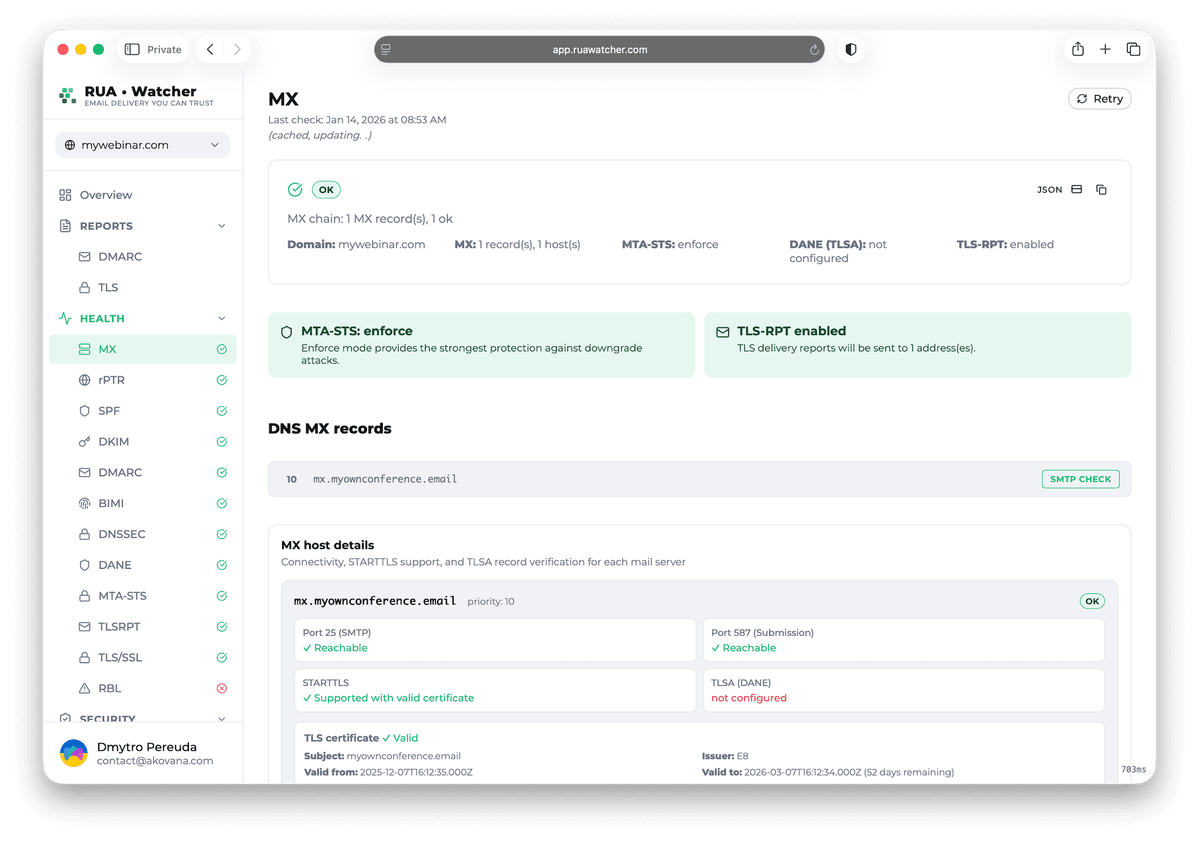
Continuously validate every selector signing mail for your domain. Discover active keys, audit cryptographic posture, and mitigate DNS-related deliverability risks before they affect your sender reputation
Automated discovery
Identify every active selector
Cryptographic auditing
Verify key strength and type
Canonicalization audit
Mitigate signature breakage
Service & stream mapping
Correlate keys to senders
Real-time alerting
Instant configuration alerts
Compliance audit trail
Historical record of changes
Optimize DKIM security in 3 steps
Discover active selectors, audit cryptographic posture, and monitor DNS to ensure seamless email signing as your infrastructure evolves
Discover selectors
Import existing selectors or leverage automated discovery to identify every active DKIM key signing mail for your domain
Audit cryptography
Verify key types, bit sizes, and signing parameters. We flag weak RSA keys and insecure configurations before they impact deliverability
Continuous monitoring
Enable real-time DNS monitoring to receive alerts for unauthorized changes, record deletions, or signature verification failures
DKIM management & security FAQ
Expert answers on DKIM selectors, cryptographic strength, signing stability, and best practices for automated key rotation
A selector is a DNS label used to locate the specific public key required for signature verification. It enables multiple services and vendors to sign mail for the same domain independently, preventing configuration conflicts.
Regular rotation limits the impact of potential private key exposure. We recommend rotating keys every 6 to 12 months, and immediately upon vendor changes, personnel turnover, or suspected security compromise.
Yes. We provide full validation for RSA (including 2048-bit and higher) and modern Ed25519 keys. We flag outdated algorithms and weak key sizes to ensure your signing posture remains secure.
Canonicalization determines how much header and body modification is tolerated during transit. Overly strict settings can cause verification failures if intermediate MTAs alter message formatting, directly impacting your DMARC alignment.
No. Your private keys remain securely within your mail servers or ESP. RUA•Watcher only monitors the public keys published in your DNS and tracks their verification health to ensure continuous security.
Ready to validate your DKIM setup?
Add your selectors, verify key strength, and get alerts when a record changes or a signature starts failing